Make Your Numbers Speak Volumes with Simple Data Visualisation for SMBs
Do you ever open up a report, scroll […]
AI Demystified:
Walk into almost any IT department right now, and you’ll hear the same conversation at least […]
Today’s businesses are no stranger to the word cybersecurity. They are facing a growing wave of cyberattacks. These come from ransomware to sophisticated phishing […]
Artificial Intelligence is no longer a technology reserved for companies with big budgets. Today, small businesses can access AI tools that help in several […]
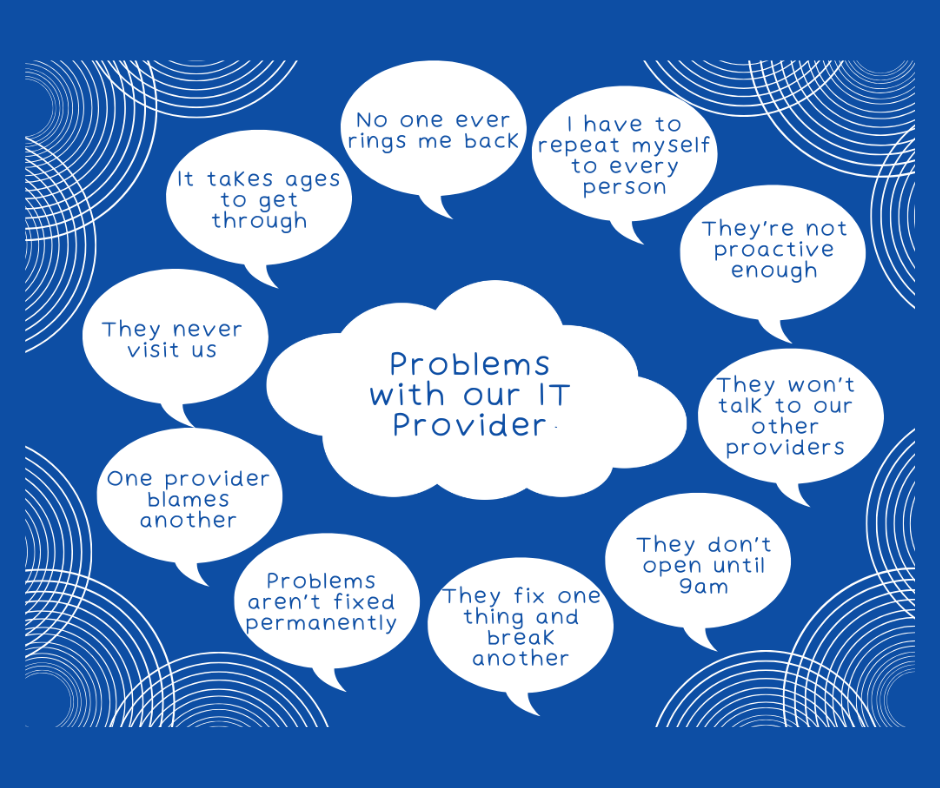
In today’s fast-paced world, having reliable IT support is critical for any business. However, many companies find themselves grappling with issues that make their […]
Data breaches are an unfortunate reality for businesses of all sizes. When a breach occurs, the immediate response is critical. How a company manages […]
Microsoft Teams continues to evolve. It is a powerful hub for collaboration and communication in the modern workplace. With the integration of AI-driven Copilot, […]