The “Deepfake CEO” Scam:
The phone rings, and it’s your boss. The voice is unmistakable; with the same flow […]
Switching IT Support providers can feel risky. Many businesses worry about downtime, data loss, missing passwords, poor handovers, or a difficult old provider. Those worries are […]
The modern office extends far beyond traditional cubicles or open-plan spaces. Since the concept of remote work became popularised in the COVID and post-COVID […]
Every growing company eventually hits a technology breaking point. Laptops slow down, servers crash, and cyber threats become a daily worry. When you realise your internal […]
AI’s Hidden Cost:
Artificial Intelligence (AI) has taken the business world by storm, pushing organisations of all sizes to […]
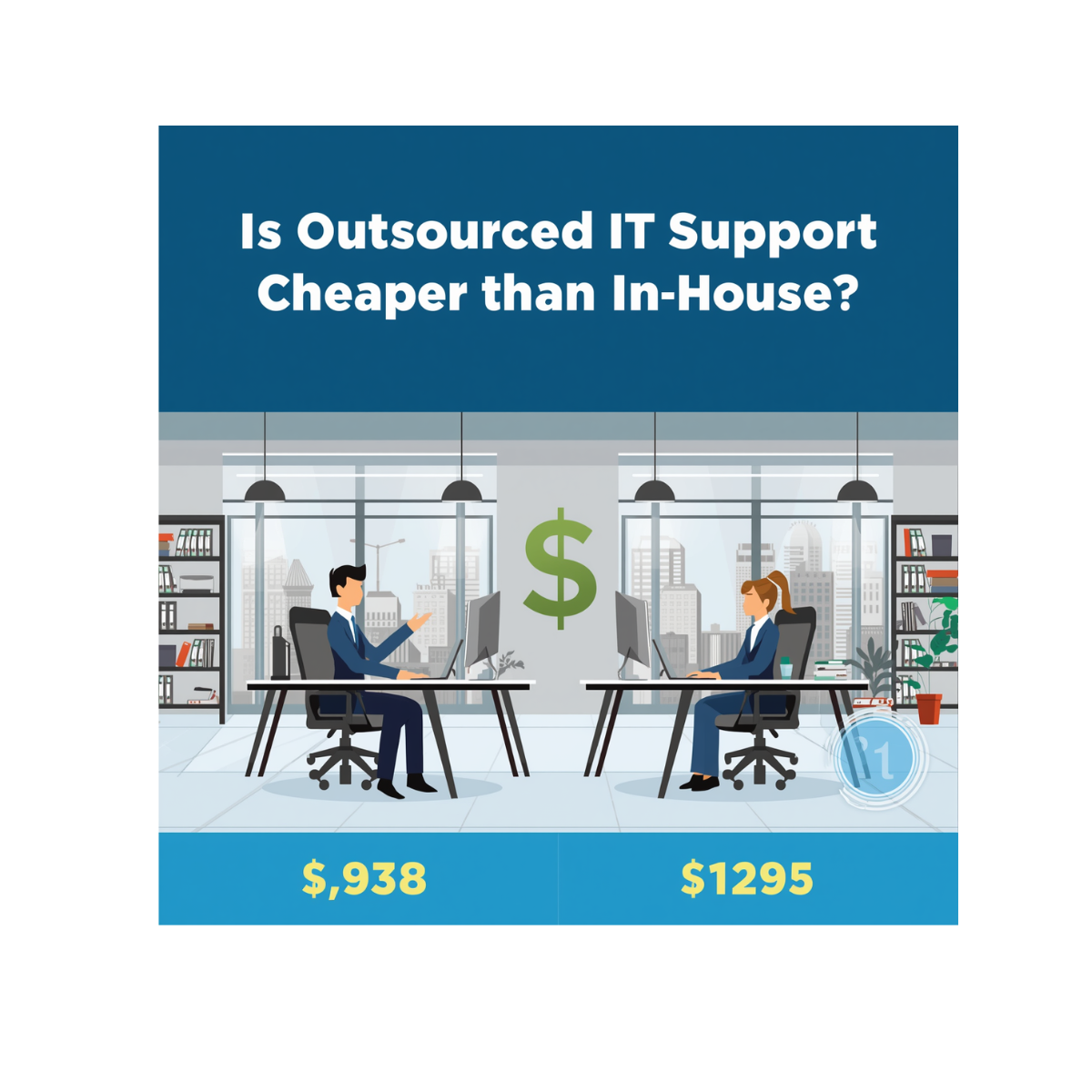
Deciding how to manage your company’s technology is one of the most critical financial choices a business owner will make. You need reliable systems, robust data […]
Your business runs on a SaaS (software-as-a-service) application stack, and you learn about a new SaaS tool that promises to boost productivity and streamline […]
When your business relies heavily on technology, an IT support agreement is not just a piece of paper; it is a vital safety net. Many businesses […]